googleapps.in.th สนใจเงินกู้ออนไลน์ผ่านแอพยืมเงินเพื่อหาเงินด่วน หรือกู้เงินนอกระบบ พร้อมทั้งมีบัตรและสินเชื่อให้เลือก
บริการเงินกู้ด่วนผ่านสินเชื่อออนไลน์หรือกู้เงินด่วนนอกระบบ และยังมีบัตรเดบิตต่างๆ และแอพยืมเงินมากมาย
สมัครกู้ยืมเงินด่วนแบบ บัตรเครดิต สินดชื่อเงินสดเหรอเงินกู้นอกระบบ กับหลายบริษัทแล้วจะได้รับผลดีกว่า
เงินกู้ออนไลน์
ต้องการสินเชื่อเงินกู้สินเชื่อส่วนบุคคลหรือกู้ยืมเงินนอกระบบผ่านแอพยืมเงินด่วนพร้อมสมัครบัตรเดบิตล่าสุด
เงินกู้ออนไลน์คืออะไร?
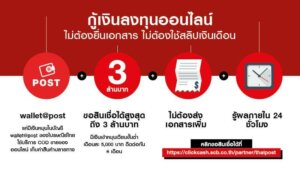
เงินกู้ออนไลน์หรือเงินกู้ออนไลน์ได้จริงคือ การที่เราต้องการเงินด่วนมาเลือกใช้บริการเพื่อหมุนเวียนเงินค่าใช้จ่ายในครอบครัวแต่เราไม่สะดวกไปเลือกใช้บริการหาเงินกู้ถึงสินเชื่อต่างๆ ถึงบริษัทเราก็ยังสามารถเลือกกู้ได้เพราะแหล่งเงินกู้ในปัจจุบันตอนนี้ไม่จำเป็นต้องไปถึงบริษัทสินเชื่อการเงินให้เสียเวลาท่านก็สามารถเลือกกู้ออนไลน์ได้แล้ว ซึ่งวันนี้ผู้เขียนจะมาแนะนำสินเชื่อออนไลน์ของแต่ละบริษัทให้ท่านทำการตัดสินใจเลือกใช้เงินกู้ออนไลน์ได้ง่ายๆ ด้วยตัวเองเราจะพาไปส่องเงื่อนไขของแต่ละบริษัทสินเชื่อส่วนบุคคล/แหล่งปล่อยเงินดอกมากันที่รูปแบบแรกคือ สินเชื่อเงินกู้ promise เป็นสินเชื่อที่ไม่ต้องใช้หลักทรัพย์ประกันใดๆ ทั้งสิ้น เงินกู้ออนไลน์รูปแบบต่อมาคือ ttbbank เป็นสินเชื่อที่ฟรีค่าธรรมเนียมแรกเข้าและมีอัตราดอกเบี้ยเพียง 3 % เท่านั้นเป็นเงินกู้ด่วนที่เหมาะแก่การช็อปปิ้งเพราะช็อปที่ไหนก็ได้ส่วนลดที่นั้นที่สำคัญสามารถเลือกช่องทางการใช้บริการผ่านแอพเงินกู้ได้ง่ายๆ ผ่านช่องทางออนไลน์
เคล็ดลับดีๆ ในการที่เราเลือกเงินกู้ออนไลน์ให้ผ่านฉลุย
- ในปัจจุบันตอนนี้หลายๆ คนคงพอที่จะทราบว่าเงินกู้ออนไลน์เปิดให้เราเลือกใช้บริการมากมายไม่ว่าจะเป็นเงินกู้ออนไลน์ได้จริง,เงินกู้ด่วนและรวมไปถึงเงินกู้ออนไลน์ถูกกฎหมาย ซึ่งผู้เขียนคิดว่าท่านยังคงไม่ค่อยทราบกันว่าแหล่งปล่อยเงินดอกมีเทคนิคง่ายๆ ให้เราสามารถเลือกกู้เงินด่วนออนไลน์และได้รับการอนุมัติภายใน 5 นาทีถ้าใครอยากทราบแล้วไปดูกันเลยรายละเอียดเกี่ยวกับเทคนิคที่ใช้ได้กับแหล่งปล่อยเงินดอก
- เทคนิคแรกที่เราสามารถใช้ได้กับเงินกู้ออนไลน์คือ เอกสารท่านต้องพร้อมในการเลือกใช้บริการ สินเชื่อเงินกู้ โดยส่วนใหญ่เอกสารที่จำเป็นต้องใช้ในการกู้เงินออนไลน์คือ สำเนาบัตรประชาชน สำเนาทะเบียนบ้านและสลิปหลักฐานเงินเดือนย้อนหลังอย่างน้อย 6 เดือน
เทคนิคที่สองที่ใช้กับการขอเงินกู้ออนไลน์คือ ไม่ควรขอสินเชื่อถี่เกินไปขั้นต่ำเราขอแนะนำให้ท่านเลือกหาเงินกู้เพียงแค่เดือนละครั้งเพราะถ้าท่านเลือกสินเชื่อนาโนอาชีพอิสระเงินกู้ดอกเบี้ยถูกบ่อยๆ มากจนเกินไปทางบริษัทจะมองว่าเราร้อนเงินและอาจจะส่งผลถึงการส่องเงื่อนไขคุณสมบัติของท่านมากขึ้นอีกด้วยในปี 2024

คุณสมบัติของผู้ที่จะสามารถเลือกใช้บริการเงินกู้ออนไลน์
คุณสมบัติของผู้ที่จะสามารถเลือกใช้บริการเงินกู้ออนไลน์รวมถึงเงินกู้ออนไลน์ได้จริงในตอนนี้คือ เราต้องขอบอกก่อนเลยว่าแต่ละแหล่งเงินกู้จะทำการกำหนดเงื่อนไขและคุณสมบัติที่แตกต่างกันออกไป ซึ่งวันนี้ผู้เขียนจะพาท่านไปทำการส่องเงื่อนไขเงินกู้ด่วนแต่ละสถานที่ให้ท่านได้ทราบและสามารถเลือกกู้เงินด่วนออนไลน์ได้ง่ายขึ้นกว่าเดิมในปัจจุบัน
- คุณสมบัติอย่างแรกที่ต้องมีในการเลือกเงินกู้ออนไลน์คือ ท่านต้องเป็นบุคคลสัญชาติไทยที่อายุ 20 ปีบริบูรณ์ขึ้นไปต้องไม่เกิน 65 ปีในตอนนี้ถึงจะสามารถเลือกเงินกู้ออนไลน์ถูกกฎหมายได้และอายุรวมระยะเวลาผ่อนชำระคืนต้องไม่เกิน 60 (ในกรณีที่ใช้คนค้ำประกันเพื่อที่จะกู้ออนไลน์)
- คุณสมบัติต่อมาที่ต้องมีในการเลือกเงินกู้ออนไลน์คือ รายได้ของท่านขั้นต่ำต้องอยู่ที่ 10,000 บาทถือเป็นขั้นต่ำของสินเชื่อออนไลน์ส่วนใหญ่ ซึ่งเราต้องขอบอกก่อนเลยว่าแหล่งปล่อยเงินดอกแต่ละที่ใช้เกณฑ์การวัดเงินเดือนเป็นหลักเพื่อคิดอัตราดอกเบี้ย
- สำหรับใครที่อยากทราบถึงขั้นตอนการสมัครใช้บริการแอพเงินกู้เพื่อใช้บริการสินเชื่อเงินกู้เราจะอธิบายให้ท่านฟังในย่อหน้าถัดไปในปี 2024 ผ่านช่องทางออนไลน์
วิธีการสมัครใช้บริการเงินกู้ออนไลน์
วิธีการสมัครใช้บริการเงินกู้ออนไลน์หรือเงินกู้ออนไลน์ได้จริงในปัจจุบันตอนนี้มีให้เราเลือกใช้บริการสินเชื่อออนไลน์ได้มากถึง 3 ช่องทาง 1.เลือกใช้บริการเงินกู้ด่วนผ่านช่องทางออนไลน์ 2.เลือกใช้บริการเงินกู้ออนไลน์ถูกกฎหมายผ่านแอพเงินกู้ และช่องทางที่ 3.ไปเลือกใช้บริการแหล่งเงินกู้ที่บริษัทสินเชื่อการเงินหรือผ่านธนาคาร
- ขั้นตอนแรกให้ท่านทำการเลือกรูปแบบสินเชื่อเงินกู้ที่ท่านต้องการ เช่น สินเชื่อฟินนิกซ์,สินเชื่อมันนี่ฮับหรือสินเชื่อส่วนบุคคลออนไลน์ถูกกฎหมาย Line bk เมื่อท่านเลือกประเภทกู้เงินออนไลน์ได้แล้วให้ท่านเข้าไปยังเว็บไซต์ของเงินกู้ออนไลน์รูปแบบที่ท่านเลือก
- ขั้นตอนต่อมาใหท่านเลือกรูปแบบเงินกู้ด่วนในแบบที่ท่านต้องการ เช่น เงินกู้ออนไลน์ถูกกฎหมายหรือจะเป็นเงินกู้ดอกเบี้ยถูก
- เมื่อทำการเลือกได้แล้วให้ท่านทำการกรอกเอกสารข้อมูลในการสมัครกับทางเงินกู้ออนไลน์ ซึ่งเอกสารที่ท่านต้องใช้คือ สำเนาทะเบียนบ้านพร้อมสำเนาบัตรประชาชนเมื่อทำการกรอกเอกสารข้อมูลกับทางแหล่งปล่อยเงินดอกที่ท่านต้องการครบแล้วให้รอการอนุมัติภายใน 2-3 วันในปี 2024 ผ่านช่องทางออนไลน์

สิทธิพิเศษที่ได้จากการเลือกใช้บริการเงินกู้ออนไลน์
สิทธิพิเศษที่ได้จากการเลือกใช้บริการเงินกู้ออนไลน์หรือเงินกู้ออนไลน์ได้จริงในตอนนี้คือ มีรูปแบบให้ท่านเลือกกู้เงินออนไลน์ได้อย่างมากมายไม่ว่าจะเป็นแหล่งปล่อยเงินดอกของธนาคารหรือจะเป็นแหล่งเงินกู้ของบริษัทสินเชื่อเงินกู้ออนไลน์ นอกจากนั้นยังไม่พอเพราะในปัจจุบันตอนนี้เงินกู้ออนไลน์มีรูปแบบให้เราเลือกใช้บริการสินเชื่อออนไลน์ได้มากถึง 3 ช่องทาง 1.เลือกใช้บริการเงินกู้ด่วนผ่านช่องทางออนไลน์ 2.เลือกใช้บริการเงินกู้ออนไลน์ถูกกฎหมายผ่านแอพเงินกู้ และช่องทางที่ 3.ไปเลือกใช้บริการแหล่งเงินกู้ที่บริษัทสินเชื่อการเงินหรือผ่านธนาคาร ซึ่งในปัจจุบันตอนนี้เงินกู้ออนไลน์ได้ทำการกำหนดคุณสมบัติสำหรับคนที่ต้องการกู้เงินออนไลน์ด่วนไว้ง่ายนิดเดียวเพียงแค่ท่านเป็นบุคคลสัญชาติไทยที่มีอายุครบ 20 ปีบริบูรณ์แล้วท่านก็เลือกใช้บริการแอปยืมเงินได้จริงได้ทันที สำหรับใครที่ต้องการอยากทราบในส่วนของอัตราดอกเบี้ยเพิ่มเติมท่านทำการส่องเงื่อนไขได้ง่ายๆ ด้วยตัวเองผ่านช่องทางออนไลน์ในปี 2024
บล็อกและบทความ

ต้องการเก็บเงิน หาดอกเบี้ยเงินฝากประจำมีที่ไหนบ้างให้เงินฝากประจำดอกเบี้ยสูง
เช็คด่วน อัพเดตดอกเบี้ยเงินฝากประจำของไทย ที่ไหนให้เงินฝากประจำดอกเบี้ยสูง 2567

มหกรรมร่วมใจแก้หนี้ตรวจสอบสถานะได้ที่ช่องทางไหนบ้าง ลงทะเบียนร่วมใจแก้หนี้
รายละเอียดโครงการมหกรรมร่วมใจแก้หนี้ ช่วยคนไทย เริ่มต้นใหม่อย่างยั่งยืน
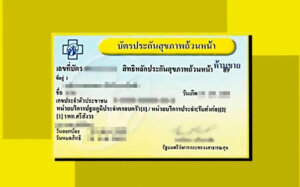
สิทธิรักษาพยาบาลบัตรทองไม่ต้องจ่ายเงินจริงไหม บัตรทองเลือกโรงพยาบาลได้ไหม
สิทธิรักษาพยาบาลบัตรทอง 2567 การรักษาพยาบาลได้อะไรบ้าง

สินเชื่อไทยพาณิชย์มีอะไรบ้าง สมัครสินเชื่อไทยพาณิชย์ผ่านแอพได้ไหม
สินเชื่อไทยพาณิชย์มีอะไรบ้าง รวมสินเชื่อไทยพาณิชย์สรุปให้เข้าใจง่ายก่อนกู้เงินไทยพาณิชย์

แหล่งเงินด่วนในการขอสินเชื่อรถจักรยานยนต์ ดอกเบี้ยรถจักรยานยนต์มือสอง
เปรียบเทียบดอกเบี้ยรถจักรยานยนต์มือสองจาก 3 แหล่งเงินด่วนชั้นนำ 2567

ผ่อนรถมือสองจะมีเคล็ดลับอย่างไรบ้าง การผ่อนชำระรถมือสองฟรีดาวน์ผ่อนถูก
ข้อดีของการผ่อนรถมือสอง (เช็คเลย)